TPRM platform: Building a defensible system beyond screening and email
When screening flags a concern, what happens next determines your defensibility. For most programs, what happens next is an email.
Trusted by 14,000+ organizations globally
































Your program has the right policies. The process breaks between them.
Risk tiering lives in a spreadsheet owned by one person. Screening flags get interpreted differently depending on who reviews them. EDD is ordered outside the platform. Reports come back to an inbox. The decision gets made – and the rationale lives absolutely nowhere permanent.
Six months later, a regulator asks how you assessed a high-risk distributor. You have the outcome. Reconstructing the methodology is what takes days.
That gap – between a decision made and a decision documented – is where TPRM programs fail scrutiny.
Three things a CCO needs to be able to do. One TPRM platform that governs all of them.
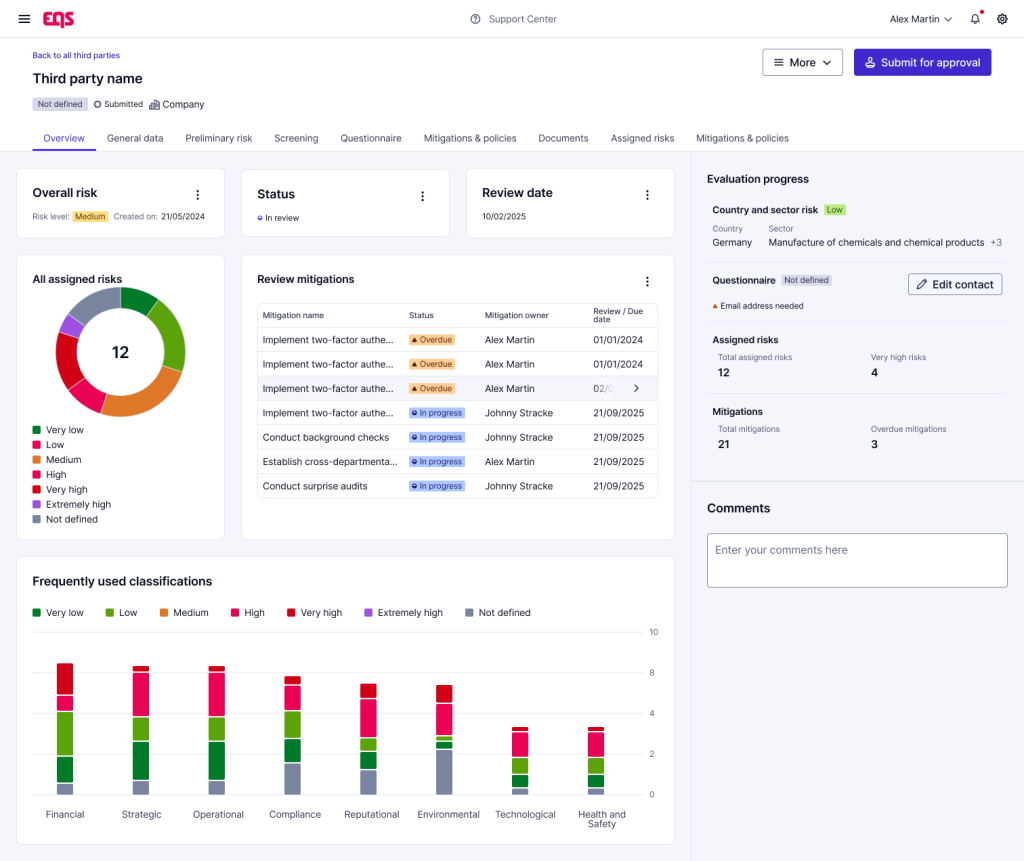
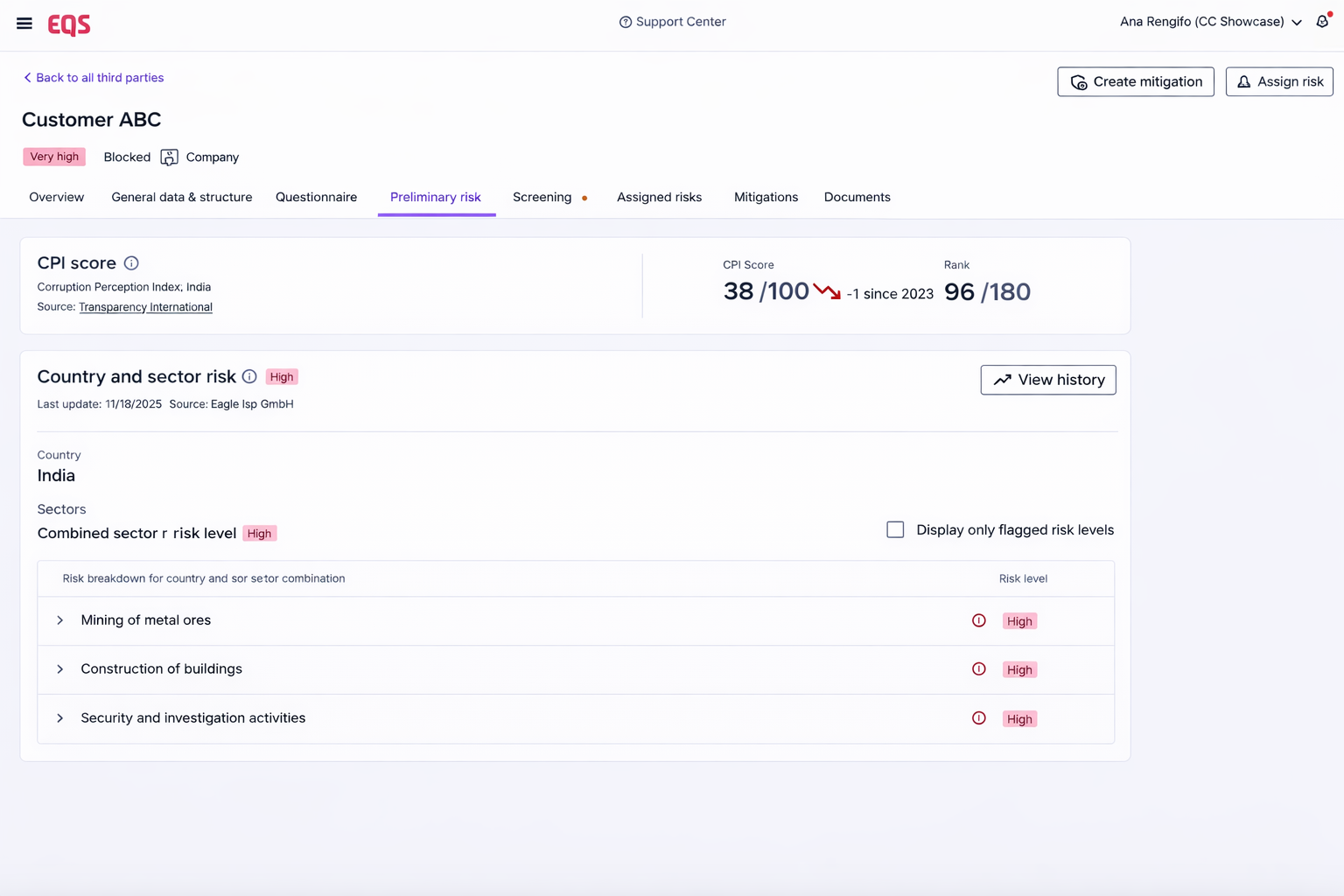
1. Apply consistent risk-based methodology across every third party — and prove it
Not a policy that says “we tier by risk.” A system that captures the tier, the basis for it, and the diligence applied — for every relationship.
2. Move escalation from email into a governed, auditable process.
When screening or a questionnaire raises a concern, the next step should be structured, documented, and stored inside the record — not dependent on who forwards what to whom.
3. Show leadership and regulators a complete picture — not a reconstructed one.
Portfolio-level visibility. Decision rationale logged at the point of decision. Mitigations with owners and completion records. A record that exists independent of the people who built it.
How EQS TPRM platform governs the third-party lifecycle
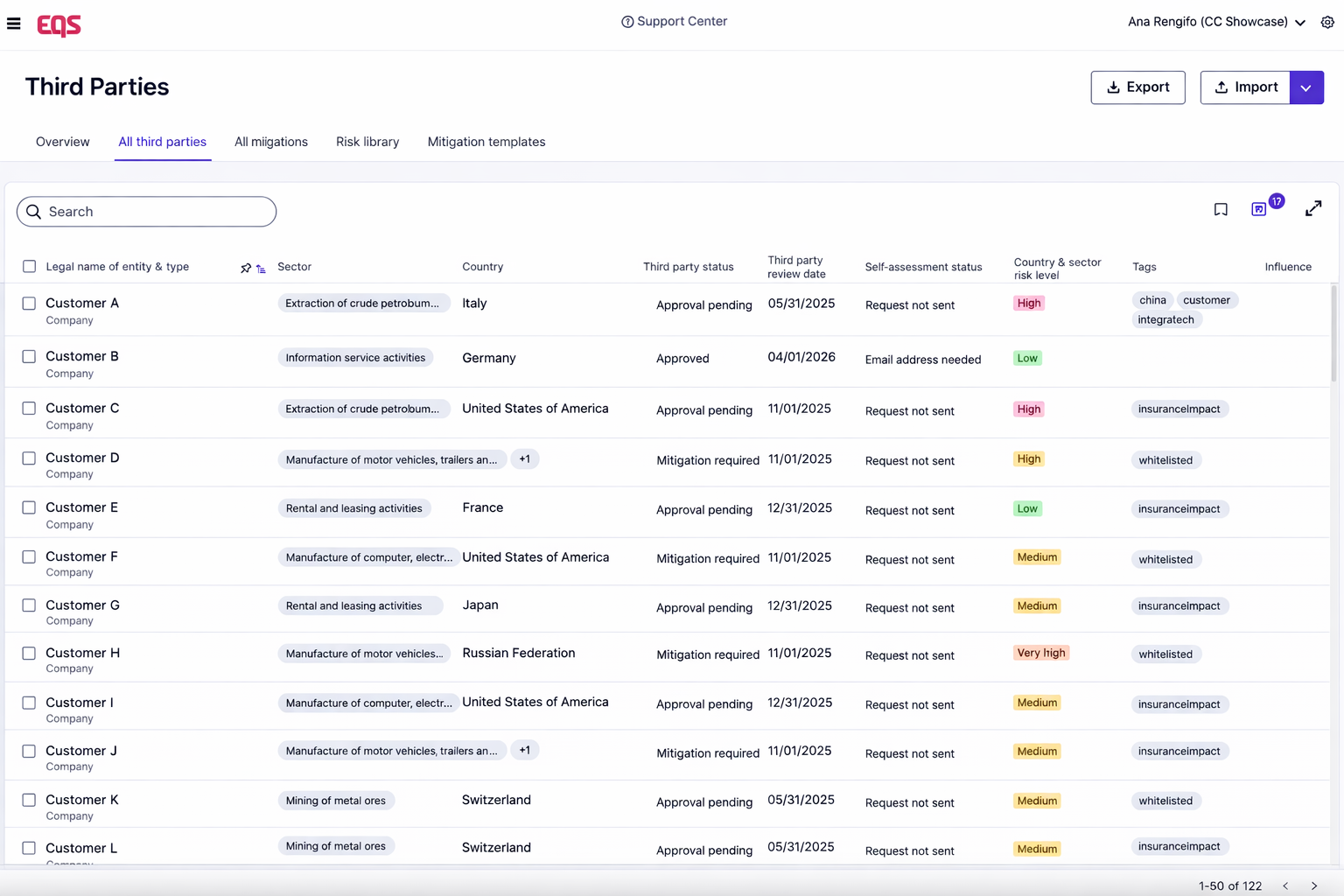
Stage 1 – Centralize and classify third parties
Your job: Apply consistent risk tiers across every third party from first contact.
What EQS does: Every third party gets a single profile. Risk tier is assigned and stored there. Classification follows a consistent framework – not the judgement of whoever opens the spreadsheet that week.
Why it matters to your program: When a regulator asks you how you classify third parties, you now have a system to show them.
Stage 2 – Screen and surface
Your job: Run baseline screening and store the results where they belong.
What EQS does: Screening runs against the third-party record. Results are stored inside that record – not exported in a folder, or forwarded to an inbox. Every flag is visible to the reviewer at the point of review.
Why it matters to your program: Screening results that live outside the record are results you may not be able to produce on request. Storage inside the profile closes that gap before it opens.
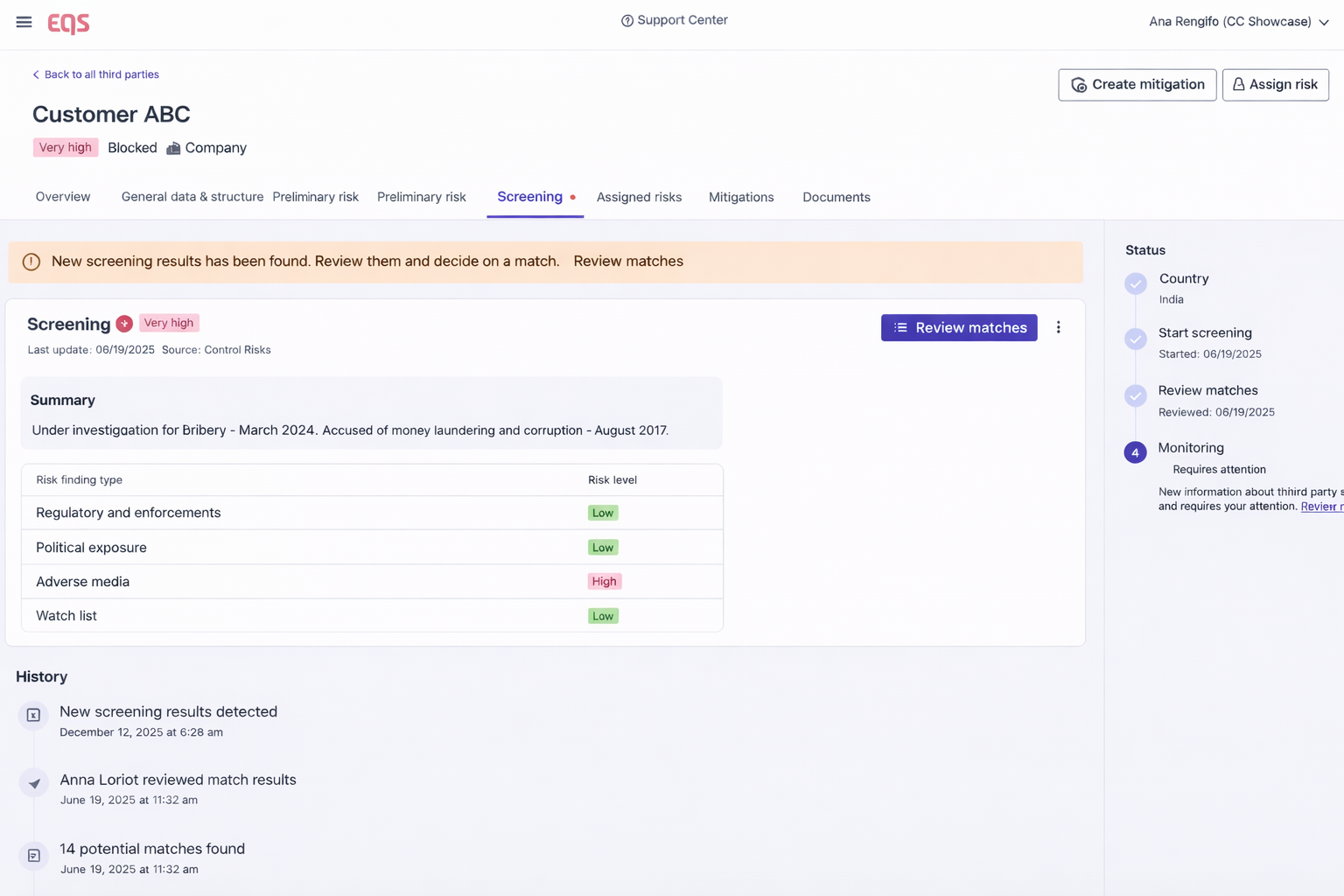
Stage 3 – Govern escalation
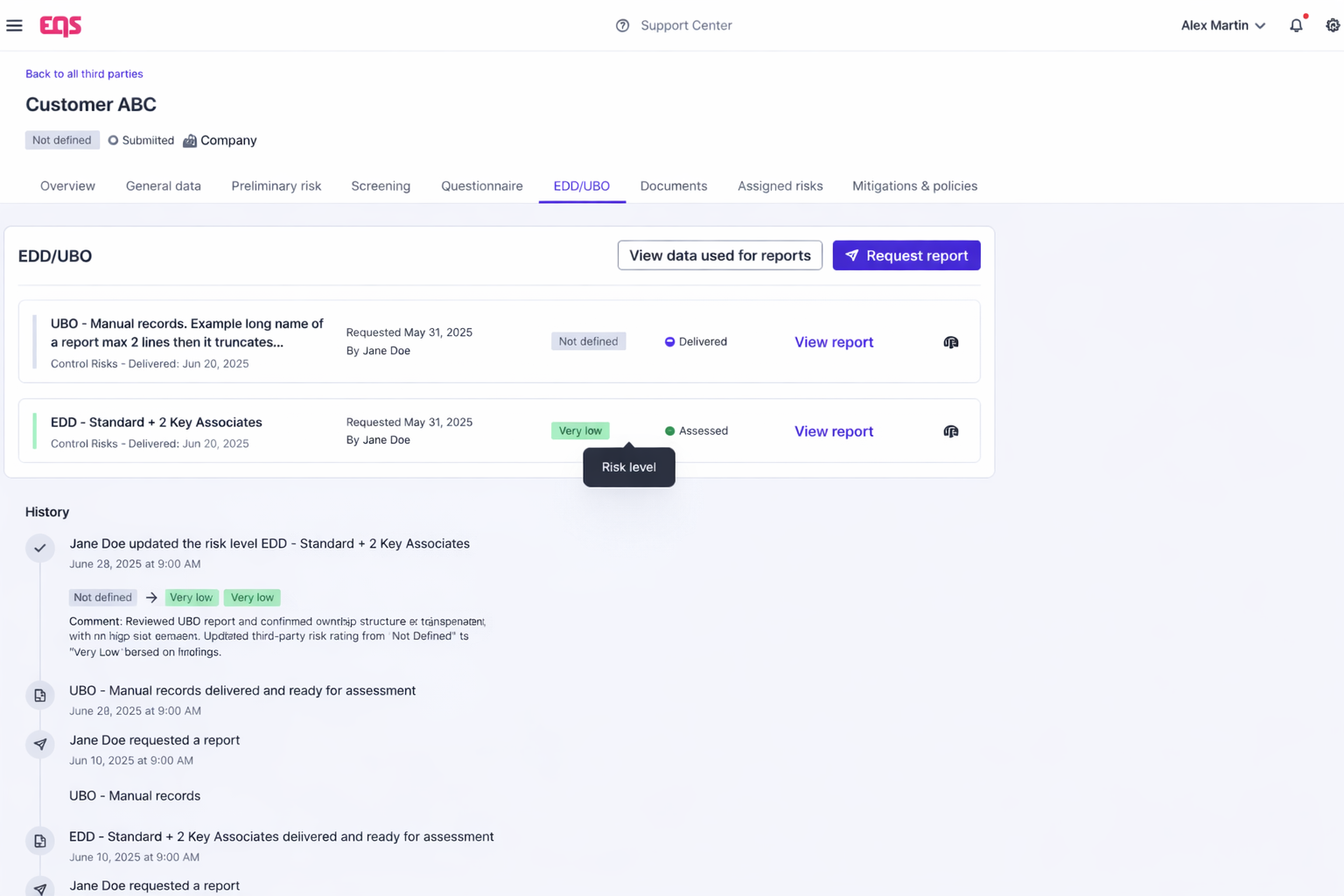
The job: Move EDD and UBO investigations out of email and into a traceable, documented process.
What EQS does: When a flag warrants escalation, EDD is initiated directly from the third-party profile. Scope is selected. Context is documented at the point of instruction. Supporting materials are attached before the request goes anywhere. The report comes back to the same record.
UBO investigations follow the same path. When self-disclosure is insufficient, an independent UBO verification is requested from inside the platform and stored inside the record that triggered it.
Why it matters to your program: The investigation chain — trigger, instruction, report, decision — stays intact. Regulators can trace it from start to finish without anyone reconstructing it.
Stage 4: Decide and log
The job: Document every approval, rejection, or conditional approval with the rationale that supported it — at the time it was made.
What EQS does: Decision outcomes are logged directly in the third-party profile. Rationale is captured in structured fields. Conditions carry assigned owners and tracked completion. The timestamp is automatic.
Why it matters to your program: A decision documented at the point it was made is evidence. A decision reconstructed six months later is a story. EQS gives you the former — consistently, across every third party.
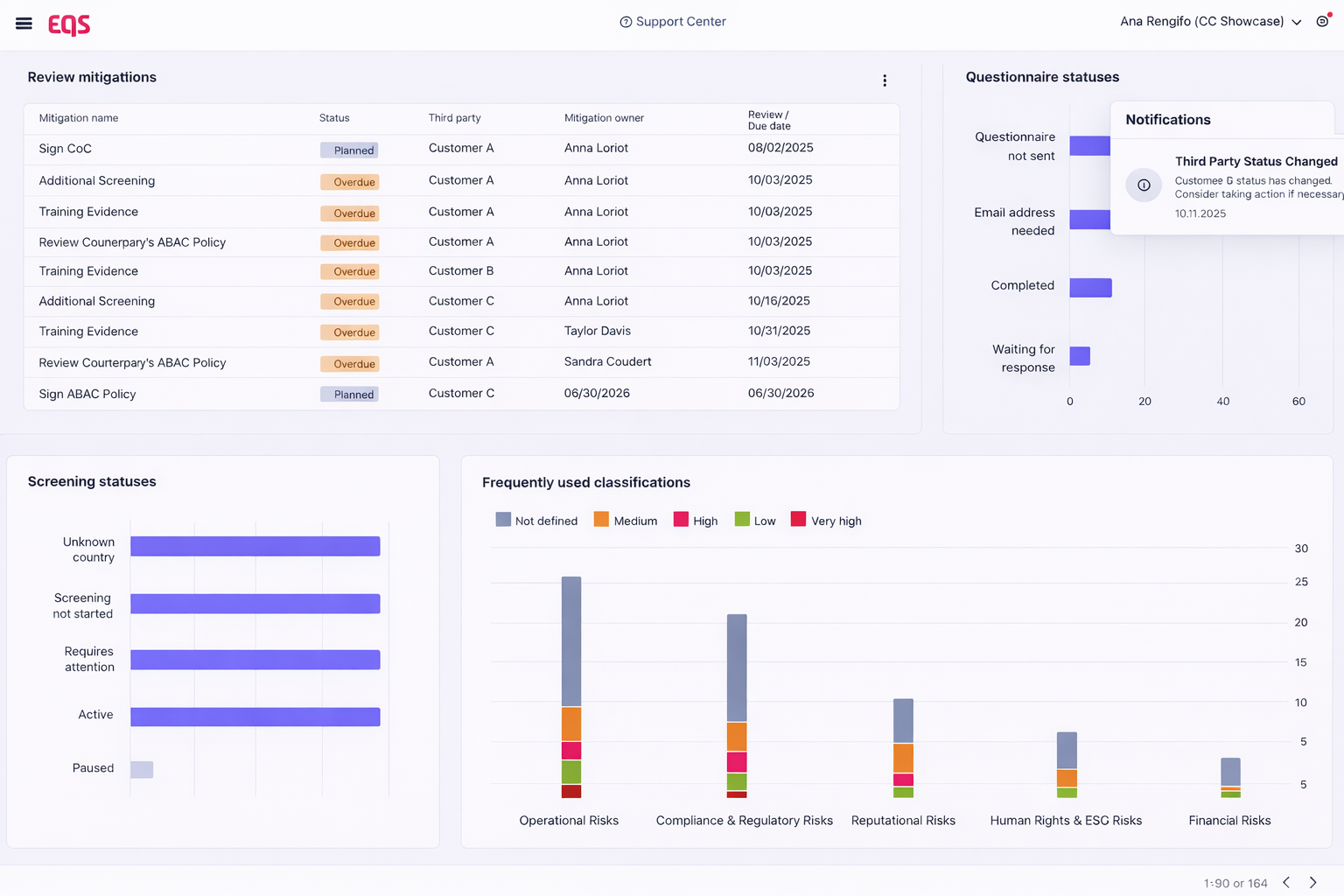
Stage 5: Maintain risk-based oversight
The job: Keep high-risk relationships under active review without consuming resources disproportionate to lower-risk vendors.
What EQS does: Review cycles are scheduled by risk tier. Screening and questionnaires refresh systematically. The portfolio view gives leadership visibility across all relationships — exposure levels, review status, outstanding mitigations — in a single view.
Why it matters to your program: Ongoing oversight with a documented schedule is a living compliance program. Reviews that only happen after incidents are evidence that the program was reactive.
What changes in measurable terms
When reporting and investigation are architected correctly:

Time to defensible decision
EDD and UBO investigations are initiated, tracked, and stored inside the platform — without the coordination overhead of managing them across email, shared drives, and separate systems.

Regulatory exposure
Every stage of the lifecycle — classification, screening, escalation, decision, oversight — generates a contemporaneous, connected record. When scrutiny arrives, the program is demonstrable. No reconstruction required.

Program scalability
Low-risk third parties clear efficiently without manual intervention. High-risk cases receive structured depth without creating bottlenecks. The program scales with the business rather than against it.
When TPRM is architected correctly:
- Low-risk third parties move faster without compromising standards.
- High-risk cases escalate in a controlled, traceable way.
- EDD and UBO reports are centralized and audit-ready.
- Mitigations are enforceable – not forgotten.
- Reviews happen systematically, not reactively.
- Leadership sees portfolio-level exposure – not disconnected files.
The program shifts from reactive due diligence to structured governance.
What your security & legal teams will need to know
- Role-based access and segregation of duties
- Full audit trail with timestamps and user attribution
- Secure document storage and controlled access
- SOC 2 Type II
Risk-Based Tiering of Third Parties: A Practical Framework for Efficient and Defensible TPRM
A five-phase model to prioritize diligence, control costs, and withstand scrutiny.
FREQUENTLY ASKED QUESTIONS
If TPRM programs fail during regulatory audits, why might they?
Most programs fail not because they missed a red flag at intake, but because they cannot reconstruct the escalation trail. If the decision-making process — such as ordering Enhanced Due Diligence (EDD) or verifying an Ultimate Beneficial Owner (UBO) — happened over fragmented email chains or shared drives, the audit trail is considered “broken.” Regulators look for contemporaneous documentation: evidence created at the time of the decision, not reconstructed months later.
How does risk-based tiering improve TPRM efficiency?
Risk-based tiering allows compliance teams to apply proportionality. By categorizing third parties into Low, Medium, and High risk, you can automate the “Green Lane” for low-risk vendors while focusing your manual resources and EDD budget on high-risk distributors or agents. The key is ensuring that the tiering logic is built into your system, not a manual spreadsheet, so that the level of diligence automatically matches the level of risk.
Why is independent UBO (Ultimate Beneficial Ownership) analysis critical for high-risk third parties?
Information provided directly by third parties may be incomplete, outdated, or structured. Independent UBO investigations go beyond self-reported data to identify the actual individuals who exert control or benefit from the entity. In a governed TPRM system, requesting this analysis should be a seamless part of the escalation workflow, with the final findings stored directly alongside the third-party profile for future auditability.
Meet our experts
 |
Matthias Zastrow VP, Sales and Compliance Solutions Specialist Matthias brings direct, cross-jurisdictional implementation experience — having guided organisations through third-party risk management program design across multiple regulatory environments. Conversations with Matthias focus on your operational reality, your regulatory exposure, and what a defensible TPRM program architecture looks like in practice. |
with a compliance expert